The Order of Resource Creations on AWS CloudFormation
- by Emre Yilmaz
- Feb 4, 2019
- AWS • DevOps • AWS CloudFormation
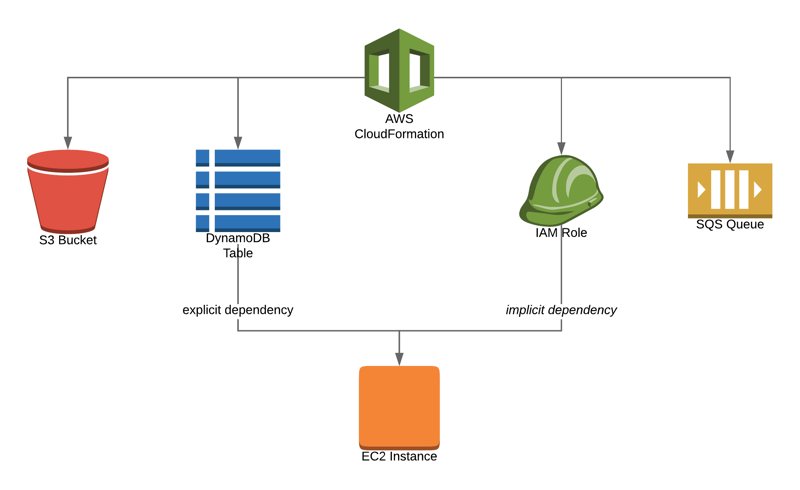
In an AWS CloudFormation template, you define independent resources or resources that are implicitly dependent; in other words, referencing other resources. For instance, you can define an Amazon EC2 instance and a security group. Then, you might choose to attach the security group to the EC2 instance or not. In these two cases, AWS CloudFormation organizes the order of the resource creations differently.
In addition, you might have another resource, such as an Amazon SNS topic in the same template, which you might want to provision after your EC2 instance is created. Maybe you have an explicit dependency between them.
In this blog post, I will talk about how AWS CloudFormation handles the order of creation for independent or implicitly dependent resources. I will also explain how to add your custom dependencies in a template.
Continue reading the The Order of Resource Creations on AWS CloudFormation blog post.